Design Space Modeling for Logic Obfuscation to Enable System-Wide Security during IC Manufacture and Test
About
Due to the rising cost of semiconductor manufacturing, computer chip designers are increasingly reliant on offshore manufacturers. These manufacturers are generally considered to be untrusted, driving concerns of intellectual property (IP) piracy and theft. Logic obfuscation, also called logic locking, was developed to mitigate these threats, however, its effectiveness varies widely based on how obfuscation resources are allocated throughout a system. This project studies how to model, automate, and evaluate the high-level configuration of logic obfuscation in a system to maximize security with minimal design overhead. The project's novelties are the system-wide view of the obfuscation resource allocation problem and the framework to generate mathematical models for this allocation problem. The purpose of these models is to automatically identify effective distributions of budgeted obfuscation resources in varied computer chips and provide intuition on how obfuscation secures a complex system. The project's broader significance and importance are in lowering the barrier to developing secure computer chips for high-trust applications (e.g., healthcare, defense, finance, and automotive) through automation. The integration of education and research is a key objective. This includes research opportunities for graduate and undergraduate students as well as open-source course modules to train next-generation security experts for the workforce.
This project bridges the knowledge gap between combinational, gate-level logic obfuscation schemes and their security impact in the larger integrated circuit they protect. Specifically, the project develops a design space modeling framework for logic obfuscation system configuration in order to budget obfuscation resources, allocate resources to design regions, and specify obfuscation schemes in these regions. Given a fixed budget of various obfuscation resources, these models automatically identify obfuscation configurations that fulfill system-wide security goals with minimal design overhead. The research artifacts are 1) quantifiable system security metrics for obfuscation, 2) an open-source design space modeling framework for obfuscation, and 3) a verification of generated models.
NSF Award Summary
NSF Award No.: #2245573
Recipient Organization: Rochester Institute of Technology
Project Period: 03/15/2023 to 02/28/2026
PD/PI: Michael Zuzak
Publications
PDF links are provided for each item below.
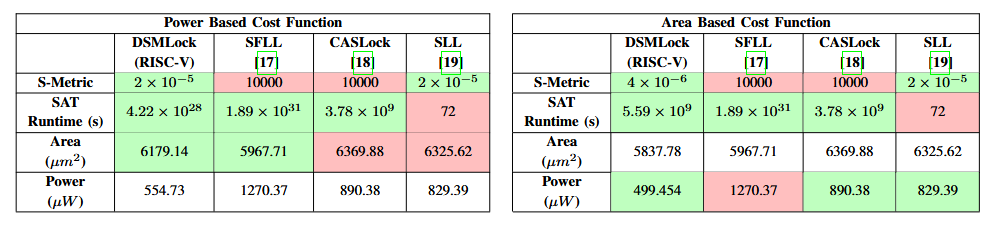
- R. Paul, L. Lam, M. Melnyk, and M. Zuzak, "DSMLock: Low Overhead Logic Locking for System Security with Design Space Modeling," IEEE Transactions on Computer-Aided Design of Integrated Circuits and Systems, Early Access, 2025. [PDF] [Code]
- R. Paul and M. Zuzak, "Michscan: Black-Box Neural Network Integrity Checking at Runtime Through Power Analysis," in 2025 IEEE International Symposium on Hardware Oriented Security and Trust (HOST), 2025, pp. 205-215. [PDF]
- T. Wojtal and M. Zuzak, "Mitigating Electro-Optical Frequency Mapping Attacks on Logic-Locked Integrated Circuits," Springer Journal of Hardware and Systems Security (JHASS), 2025. [PDF] [Code]
- L. Lam, M. Melnyk, and M. Zuzak, "Low Overhead Logic Locking for System-Level Security: A Design Space Modeling Approach," in IEEE/ACM International Symposium on Low Power Electronic Design (ISLPED), 2024, pp. 1-6. [PDF]
- K. Nakano, M. Zuzak, C. Merkel, and A. Loui, "Trustworthy and Robust Machine Learning for Multimedia: Challenges and Perspectives," in IEEE International Conference on Multimedia Information Processing and Retrieval (MIPR), 2024. [PDF]
- M. Zuzak, Y. Liu, and A. Srivastava, "Security-Aware Resource Binding to Enhance Logic Obfuscation," IEEE Transactions on Computer-Aided Design of Integrated Circuits and Systems, vol. 42, no. 12, pp. 4528-4540, 2023. [PDF]
- H. Xu, D. Liu, C. Merkel, and M. Zuzak, "Exploiting Logic Locking for a Neural Trojan Attack on Machine Learning Accelerators," in GLSVLSI '23: Proceedings of the Great Lakes Symposium on VLSI 2023, 2023, pp. 351-356. [PDF]
Open-Source Tooling and Teaching Resources
Research Tools
- Design Space Modeling for Logic Locking: An open-source example script implementing DSMLock for logic-locked ICs. Provides a Python interface to R functions, including SSANOVA modeling. An overview of the algorithm is in the ISLPED'24 paper above.
- Adjoining Gates: An open-source set of functions to detect key leakage from electro-optical frequency mapping attacks in logic-locked circuits and implement Adjoining Gates as a countermeasure. An overview is in the JHASS'25 paper above.
Teaching Resources
CMPE361: Introduction to Hardware Security: An undergraduate hardware security course developed under this project and offered at RIT since Fall 2023. New York State approved the course as the required first course for the new Secure Systems degree option in Computer Engineering, which launched in Fall 2024.
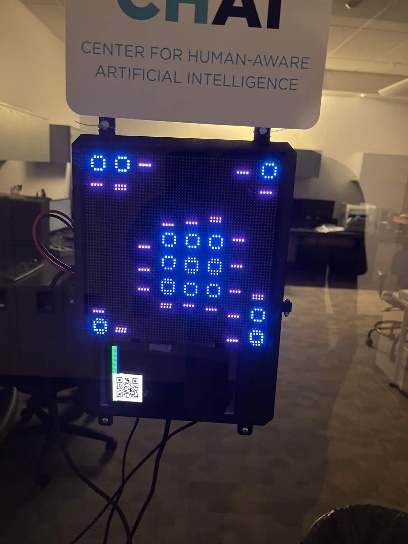
RenCTF: An interactive, team-based platform for teaching penetration testing skills, combining a web application with a hardware component. Developed by RenAaron Ellis and Dr. Zuzak. More than 85 RIT students have participated in capture-the-flag-style cybersecurity exercises on the platform. An updated UI and AI co-pilot were developed through NSF Award No. 2344237.
Student Researchers
- Robi Paul: PhD Student Researcher
- Maksym Melnyk: PhD Student Researcher
- Long Lam: MS Student Researcher (graduated May 2024)
- Thomas Wojtal: MS Student Researcher (graduated May 2024)
- Sydale John Ayi: MS Student Researcher (graduated May 2025)
- RenAaron Ellis: Undergraduate Student Researcher
Graduate Theses
- Long Lam, Low Power Logic Locking using Design Space Modeling to Achieve System-Wide Security, MS Thesis, Rochester Institute of Technology, May 2024. [RIT Repository]
- Thomas Wojtal, Adjoining Gates: Mitigating Optical Side-Channel Attacks on Integrated Circuits through Security-Aware Placement, MS Thesis, Rochester Institute of Technology, May 2024. [RIT Repository]
Project Figures and Experimental Results
DSMLock: Design Space Modeling Framework
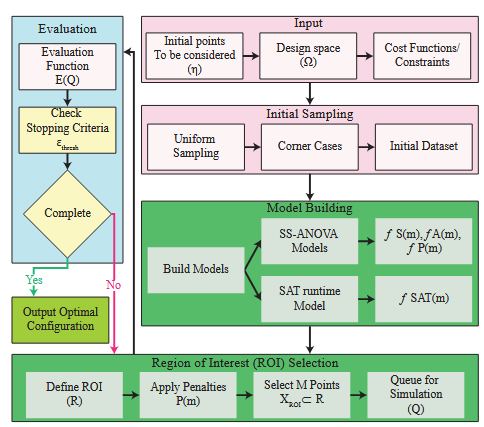
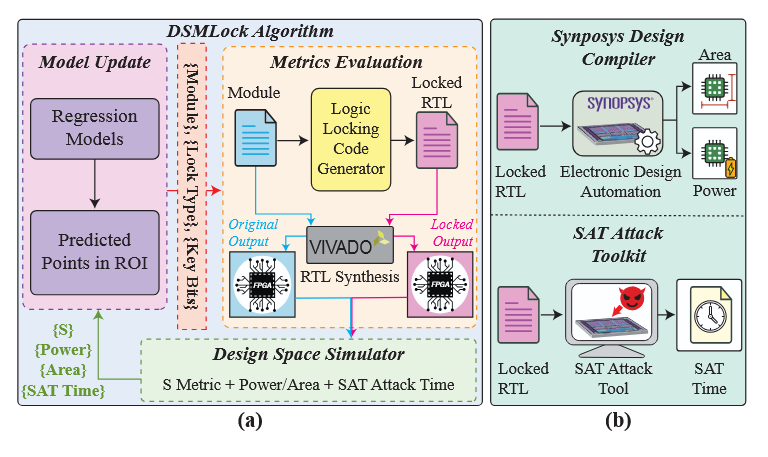
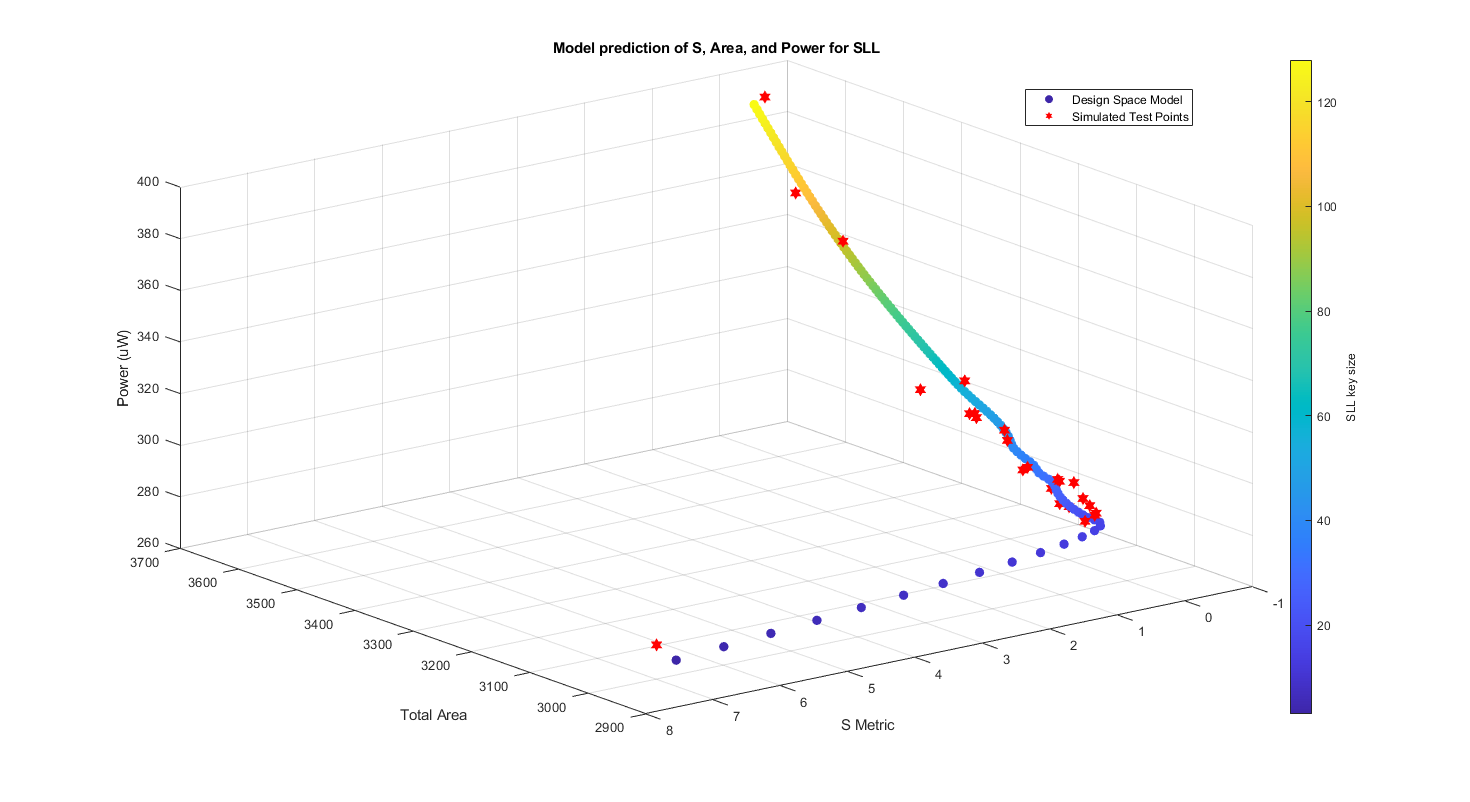
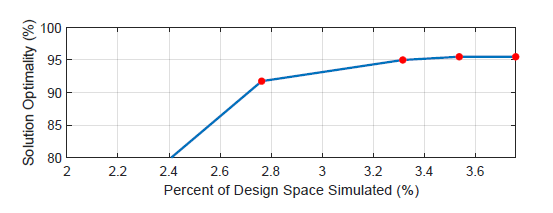
DSMLock iteratively samples the locking design space, builds predictive models of design objectives, and identifies locking configurations for designer-specified cost functions.
RenCTF Workforce Development Platform
RenCTF is an interactive security exhibit deployed in the Kate Gleason Engineering building at RIT. The platform hosts team-based capture-the-flag-style cybersecurity exercises. An AI co-pilot was developed for the platform through NSF Award No. 2344237.

Contact
- Michael Zuzak, Assistant Professor, Department of Computer Engineering, Rochester Institute of Technology: mjzeec@rit.edu
Acknowledgment

This material is based upon work supported by the National Science Foundation under NSF Award No. #2245573.
Any opinions, findings and conclusions or recommendations expressed in this material are those of the author(s) and do not necessarily reflect the views of the National Science Foundation.
